What Is Bearer Tokens for REST APIs and How to Debug It With Code & Tools
In this guide, we will delve into the concept of bearer tokens for REST APls, exploringtheir purpose, implementation, and common debugging techniques using code andspecialized tools.
Bearer tokens play a crucial role in securing and authorizing access to REST APIsserving as a form of authentication that grants users permission to interact withprotected resources. in the world of web development, understanding how beareltokens work and being able to effectively debug issues related to them is essentialfor maintaining the security and functionality of APl-driven applications.

In this guide, we will delve into the concept of bearer tokens for REST APls, exploringtheir purpose, implementation, and common debugging techniques using code andspecialized tools.
Why Use Bearer Tokens for REST APIs
Bearer tokens are a popular authentication mechanism for REST APIs due to their simplicity and security. They serve as a method of conveying user credentials in HTTP requests, ensuring that only authorized users can access specific resources.
Advantages:
Statelessness: Bearer tokens allow for stateless authentication, where the server doesn’t need to keep track of user sessions.
Flexibility: They can be easily integrated with different backend services and scale horizontally more efficiently.
Secure: By using protocols like HTTPS, bearer tokens can securely transmit user identity without exposing sensitive data.
What is a Bearer Token?
A bearer token is a type of access token that is used in OAuth 2.0 authentication protocols. It is essentially a string that the client sends to the server to authenticate itself. If a request includes a valid bearer token, the server grants access to the requested resources.
Structure:
Bearer tokens can vary in structure but are typically long, randomized strings that offer sufficient entropy to be secure against brute-force attacks. They can also include metadata, such as expiration times and scopes of access.
How to Implement Bearer Token in Java
To implement bearer token authentication in a Java REST API, you can follow these steps:
Step 1: Generate a Token
import io.jsonwebtoken.Jwts;
import io.jsonwebtoken.SignatureAlgorithm;
public String generateToken(String username) {
return Jwts.builder()
.setSubject(username)
.setExpiration(new Date(System.currentTimeMillis() + 86400000)) // 1 day expiration
.signWith(SignatureAlgorithm.HS256, "secret-key")
.compact();
}
Step 2: Use the Token in Requests
In your controller, retrieve the token from the Authorization header:
import javax.servlet.http.HttpServletRequest;
public void someEndpoint(HttpServletRequest request) {
String authHeader = request.getHeader("Authorization");
if (authHeader != null && authHeader.startsWith("Bearer ")) {
String token = authHeader.substring(7);
// Validate token here
}
}
Step 3: Validate the Token
public Claims validateToken(String token) {
return Jwts.parser()
.setSigningKey("secret-key")
.parseClaimsJws(token)
.getBody();
}
How to Use Tools to Test Bearer Tokens
Testing bearer token authentication can be done using various tools like Postman or cURL.
Using EchoAPI:
1.Open EchoAPI and create a new request.
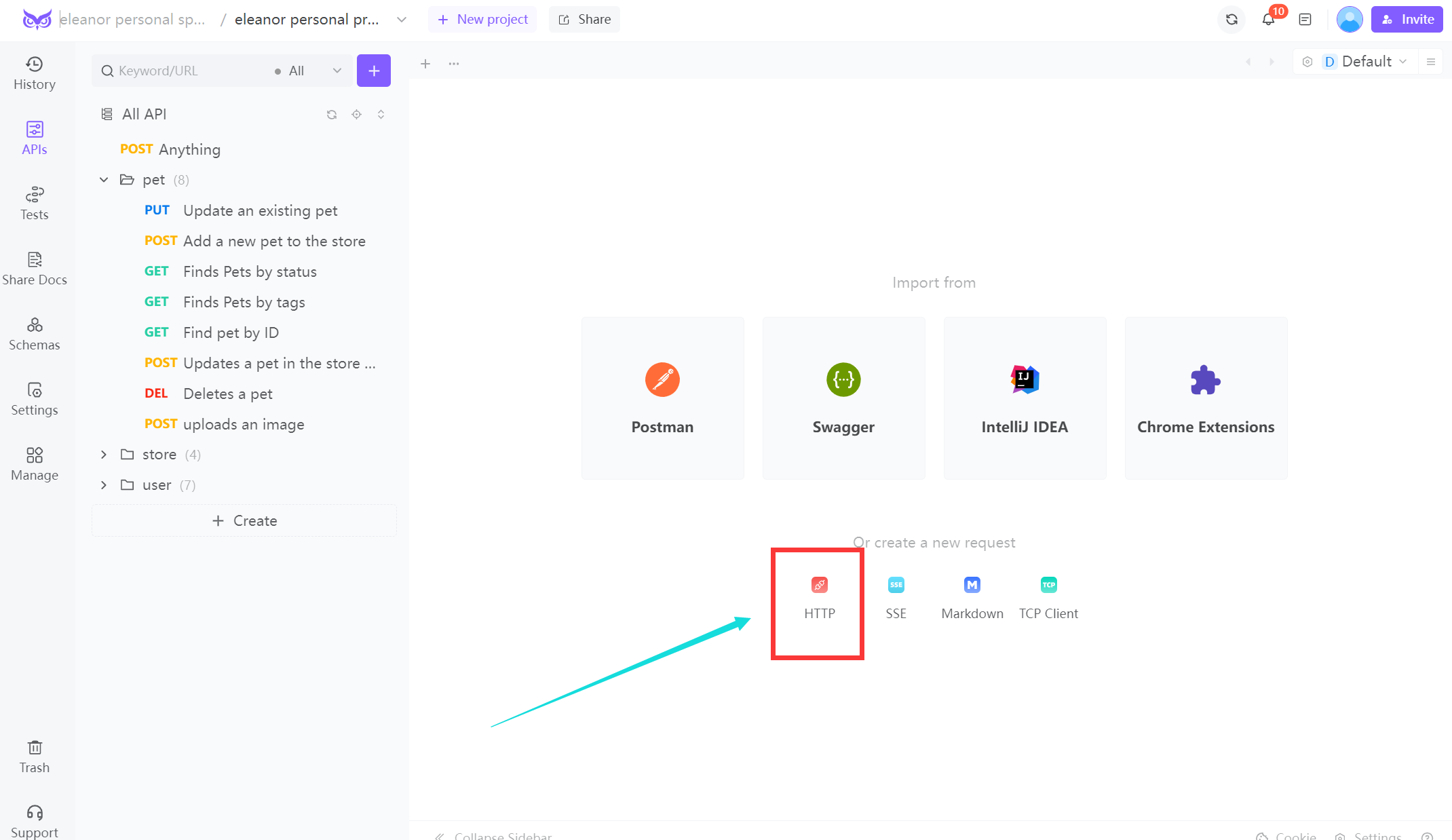
2.Select the HTTP method (GET, POST, etc.) and enter the request URL.
3.Navigate to the "Authorization" tab.
4.Choose "Bearer Token" from the dropdown.
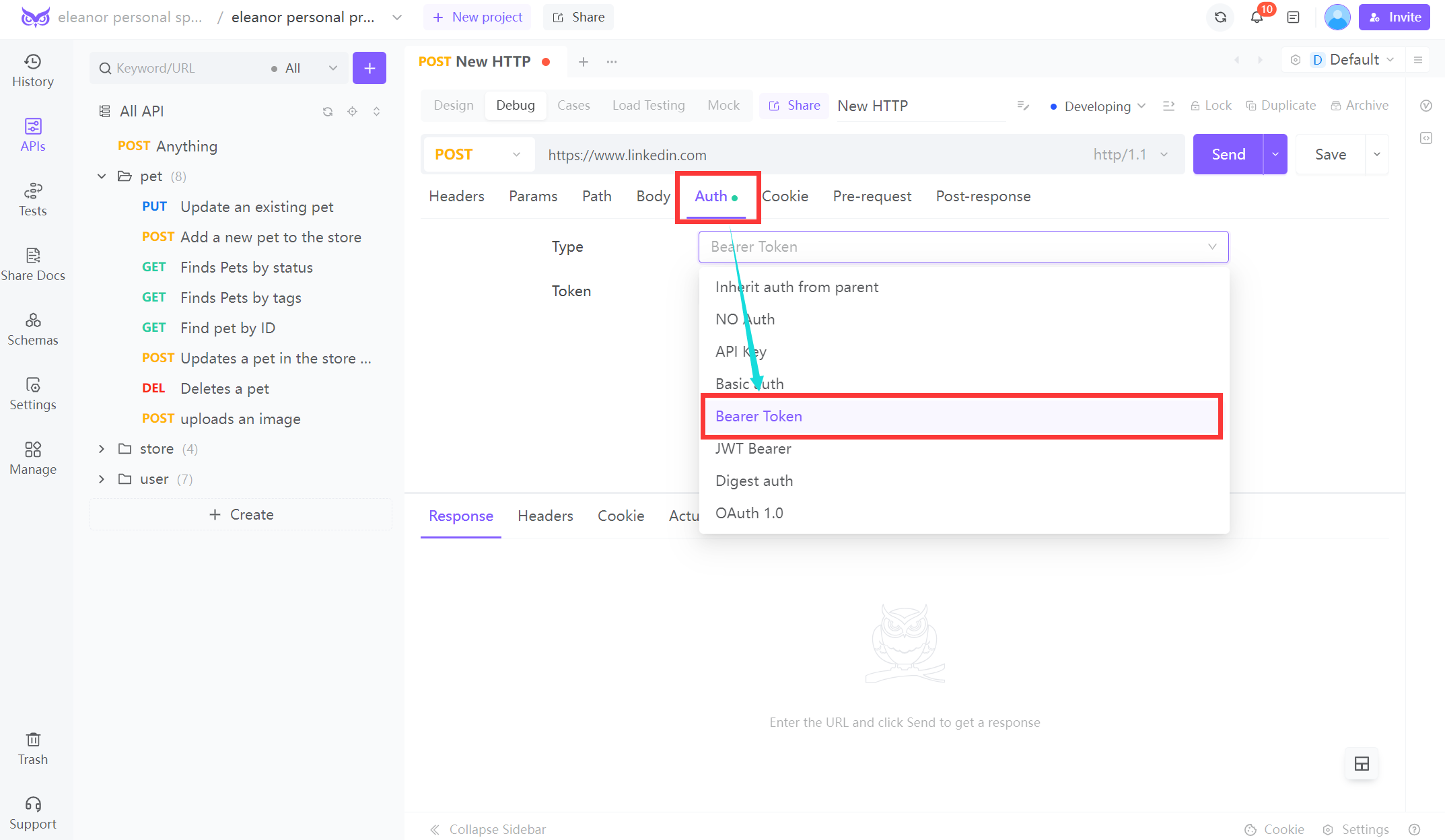
5.Enter your token in the provided field.
6.Send the request and check the response.
Using cURL:
You can also use cURL to test your API with a bearer token:
curl -X GET http://api.example.com/endpoint \
-H "Authorization: Bearer your_token_here"
Conclusion
Bearer tokens provide a robust and flexible method for authenticating users in REST APIs. By implementing bearer token authentication in Java, you ensure that your API is secure and efficient. With tools like Postman and cURL, testing these tokens becomes straightforward, allowing developers to verify that only authorized users can access specific resources. As the need for secure, scalable API solutions grows, understanding and effectively implementing bearer tokens will remain a critical skill for any backend developer.




 EchoAPI for VS Code
EchoAPI for VS Code

 EchoAPI for IntelliJ IDEA
EchoAPI for IntelliJ IDEA

 EchoAPl-Interceptor
EchoAPl-Interceptor

 EchoAPl CLI
EchoAPl CLI
 EchoAPI Client
EchoAPI Client API Design
API Design
 API Debug
API Debug
 API Documentation
API Documentation
 Mock Server
Mock Server